Best Data Protection For Companies: Ensuring Cybersecurity And Compliance
In the realm of data protection for companies, ensuring cybersecurity and compliance is paramount. From implementing robust encryption to managing risks effectively, this topic delves into the essential strategies that organizations need to safeguard their data and reputation.
As we navigate through the intricate landscape of cybersecurity and legal compliance, it becomes evident that a proactive approach is key to mitigating potential threats and vulnerabilities.
Methods of Cybersecurity Protection
In today’s digital age, organizations must implement robust cybersecurity protection methods to safeguard their sensitive data and prevent cyber threats. From encryption to security audits, here are some key strategies used by companies:
End-to-End Encryption
- Implement strong encryption algorithms to secure data both at rest and in transit.
- Utilize encryption keys and secure protocols to protect information from unauthorized access.
- Ensure all communication channels and storage systems are encrypted to maintain data integrity.
Regular Security Audits
- Conduct routine security audits to identify vulnerabilities and weaknesses in the organization’s systems.
- Engage third-party cybersecurity experts to perform comprehensive audits and penetration testing.
- Address any security gaps promptly and update security measures to mitigate risks effectively.
Risk Management in IT Security
Effective risk management is crucial in maintaining a strong IT security posture. Here’s how organizations can manage cyber risks:
Risk Assessment Process
- Evaluate potential cyber threats and vulnerabilities that could impact the organization’s operations.
- Analyze the likelihood and impact of each risk to prioritize mitigation efforts effectively.
- Develop risk mitigation strategies to reduce the likelihood of cyber incidents and their impact on the business.
Risk Mitigation Strategies
- Implement robust access controls and authentication mechanisms to prevent unauthorized access to critical systems.
- Regularly update software and security patches to address known vulnerabilities and protect against cyber threats.
- Train employees on cybersecurity best practices to create a security-aware culture within the organization.
Incident Response Planning
Incident response planning is essential for effectively handling cybersecurity incidents. Here’s how companies can create a comprehensive incident response plan:
Key Components of Incident Response Plan
- Establish a dedicated incident response team with defined roles and responsibilities.
- Develop detailed incident response procedures outlining steps to detect, contain, eradicate, and recover from security incidents.
- Regularly test the incident response plan through tabletop exercises and simulations to ensure readiness.
Secure Software Development Practices
Integrating security measures into the software development lifecycle is critical for building secure applications. Here are some best practices for secure software development:
Secure Coding and Testing
- Follow secure coding guidelines to prevent common vulnerabilities such as SQL injection and cross-site scripting.
- Conduct regular security code reviews and testing to identify and remediate security flaws early in the development process.
- Integrate security tools and automation into the development pipeline to ensure continuous security testing and validation.
Legal Compliance
Ensuring legal compliance with data protection regulations is crucial for companies to safeguard customer information and maintain trust. Non-compliance can lead to severe financial penalties and irreparable damage to a company’s reputation. It is essential for organizations to adhere to various data protection laws, such as the General Data Protection Regulation (GDPR) in the EU, the California Consumer Privacy Act (CCPA) in the United States, and the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada.
Data Security Measures
- Encryption methods play a vital role in protecting sensitive data by converting it into a secure format that can only be accessed with the appropriate decryption key.
- Access control mechanisms help in maintaining data security by limiting access to sensitive information only to authorized personnel.
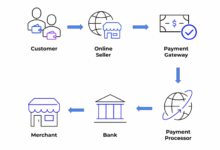
- Companies can implement security protocols like SSL/TLS (Secure Sockets Layer/Transport Layer Security) and VPNs (Virtual Private Networks) to secure their data during transmission and storage.
Incident Response Planning
Developing an effective incident response plan involves several key steps to mitigate the impact of data breaches. Communication strategies are crucial in handling incidents promptly and transparently. Companies can create an incident response plan by following a structured framework that includes identifying key stakeholders, assessing risks, establishing response procedures, conducting regular drills, and continuously updating the plan to address emerging threats.
Data Encryption
Data encryption plays a crucial role in safeguarding sensitive information for companies by converting data into a secure format that can only be accessed with the appropriate decryption key. This helps prevent unauthorized access to data and maintains its confidentiality and integrity.
Encryption Methods
- Symmetric Encryption: Involves using the same key to encrypt and decrypt data, making it faster but requiring secure key distribution.
- Asymmetric Encryption: Uses a pair of public and private keys for encryption and decryption, enhancing security but being slower than symmetric encryption.
- Hashing: Converts data into a fixed-length string of characters, making it irreversible and ideal for verifying data integrity.
- Hybrid Encryption: Combines symmetric and asymmetric encryption methods for a balanced approach to security and efficiency.
Importance of Encryption
Encryption is vital in protecting data during transmission over networks and storage in databases or cloud servers. It helps prevent data breaches, unauthorized access, and ensures compliance with regulations such as GDPR and HIPAA. Encryption also safeguards intellectual property and sensitive information in industries like healthcare, finance, and e-commerce.
Access Control
Access control refers to the process of regulating who can access certain resources or information within a system. In the context of data protection, access control plays a crucial role in preventing unauthorized users from gaining access to sensitive data.
Implementing access control mechanisms within a company’s data storage systems is essential to ensure that only authorized individuals can view, modify, or delete data. By setting up access control, organizations can minimize the risk of data breaches and unauthorized access, thus safeguarding their valuable information.
Access Control Strategies
- Role-Based Access Control (RBAC): RBAC assigns permissions based on job roles, ensuring that individuals have access only to the data necessary for their specific role.
- Attribute-Based Access Control (ABAC): ABAC evaluates various attributes before granting access, such as user location, time of access, and device used, to determine authorization.
- Discretionary Access Control (DAC) vs. Mandatory Access Control (MAC): DAC allows data owners to set access permissions, while MAC is more rigid, with access determined by security labels assigned by administrators.
Access control lists (ACLs) are commonly used to manage permissions for resources by listing which users or groups have access to specific files or directories. ACLs help enforce security policies and ensure that access rights are granted appropriately.
In summary, access control is a vital component of data protection, and companies can enhance their security measures by implementing various access control strategies tailored to their specific needs and requirements.
Regular Data Backups
Regular data backups are crucial for companies to protect their data from loss or corruption. By regularly backing up their data, companies can ensure that they have a copy of their information in case of a cyberattack, hardware failure, or accidental deletion.
Best Practices for Data Backup Strategy
- Frequency of Backups: Companies should schedule backups regularly, depending on the volume of data changes. Daily or weekly backups are common practices.
- Types of Backups: Implement a combination of full, incremental, and differential backups to optimize storage and recovery times.
- Storage Options: Consider storing backups both on-premises and in the cloud for added redundancy and security.
Tools for Automated Data Backups
- Veeam: Offers comprehensive backup and recovery solutions with features like data deduplication and encryption.
- Acronis: Known for its reliable backup software that supports multiple platforms and devices.
- Backup Exec: Provides backup and recovery capabilities for both physical and virtual environments.
Comparison Table of Data Backup Solutions
| Tool | Features | Pricing | Compatibility |
|---|---|---|---|
| Veeam | Advanced data deduplication and encryption | Subscription-based pricing | Supports various operating systems |
| Acronis | Reliable backup software for multiple platforms | Perpetual license options | Compatible with physical and virtual environments |
| Backup Exec | Backup and recovery for diverse environments | Flexible pricing plans | Works with both physical and virtual servers |
Setting up Automated Backup Schedule
- Choose a suitable backup tool like Veeam, Acronis, or Backup Exec based on your company’s needs.
- Install the software on your systems and configure the backup settings, including backup frequency and storage location.
- Set up an automated backup schedule to run at convenient times when the system is least active to avoid performance impact.
- Monitor the backup process regularly to ensure that all critical data is being backed up successfully.
Employee Training
Employee training plays a critical role in ensuring data protection within a company. By educating employees about cybersecurity best practices, companies can significantly reduce the risks of data breaches and unauthorized access to sensitive information.
Employee awareness and education are crucial for maintaining data security because human error and negligence are among the leading causes of data breaches. When employees are well-informed about the importance of data protection and the potential risks associated with cyber threats, they are more likely to follow security protocols and take the necessary precautions to safeguard company data.
Examples of Data Protection Training Programs
- Regular Security Awareness Workshops: Companies can conduct regular workshops to educate employees about the latest cybersecurity threats, best practices for data protection, and how to identify phishing attempts.
- Simulated Phishing Exercises: Organizations can simulate phishing attacks to test employees’ responses and provide immediate feedback on how to recognize and avoid phishing emails.
- Data Handling Training: Employees should receive training on proper data handling procedures, including how to securely store, share, and dispose of sensitive information.
- Role-Specific Training: Different departments may require specialized training based on their roles and access levels to ensure that employees understand their responsibilities in protecting company data.
Incident Response Plan
An incident response plan is a structured approach that organizations follow when dealing with a cybersecurity incident. It outlines the steps to be taken to detect, respond to, and recover from security breaches or data incidents. Having an incident response plan is crucial for companies as it helps minimize the impact of a breach, reduce recovery time, and maintain business continuity.
Key Components of an Effective Incident Response Plan
- Identification and Classification of Incidents: Clearly define what constitutes a security incident and categorize them based on severity.
- Response Team and Communication Plan: Establish a dedicated team responsible for managing incidents and define communication protocols internally and externally.
- Containment and Eradication Procedures: Implement measures to contain the incident, prevent further damage, and eliminate the root cause.
- Evidence Collection and Analysis: Gather evidence to understand the scope of the incident and analyze the impact on systems and data.
- Recovery and Restoration Strategies: Develop strategies to restore affected systems and data to normal operations while ensuring security.
Testing and Improving Incident Response Procedures
Companies can test and improve their incident response procedures through:
- Tabletop Exercises: Simulate different scenarios to test the effectiveness of the response plan and identify areas for improvement.
- Penetration Testing: Conduct regular penetration tests to identify vulnerabilities and assess the organization’s ability to detect and respond to attacks.
- Post-Incident Reviews: Analyze past incidents to identify gaps in the response plan and make necessary adjustments for better preparedness.
- Continuous Training and Education: Provide ongoing training to response team members and employees to ensure they are equipped to handle security incidents effectively.
Data Loss Prevention
Data loss prevention is a crucial aspect of cybersecurity for companies, as it involves implementing strategies and tools to safeguard sensitive data from unauthorized access, disclosure, or theft. By proactively preventing data loss, organizations can protect their reputation, avoid legal repercussions, and maintain the trust of their customers and stakeholders.
Strategies and Tools for Data Loss Prevention
- Implementing data loss prevention (DLP) software to monitor and control data transfers within and outside the organization.
- Establishing clear data security policies and guidelines for employees to follow, including restrictions on sharing sensitive information.
- Using encryption technologies to secure data at rest and in transit, reducing the risk of unauthorized access or data breaches.
- Regularly conducting security assessments and audits to identify vulnerabilities and gaps in data protection measures.
Role of Employee Training in Data Loss Prevention
Employee training plays a crucial role in implementing data loss prevention measures, as employees are often the first line of defense against data breaches. By educating staff on data security best practices, recognizing phishing attempts, and understanding the importance of safeguarding sensitive information, organizations can enhance their overall cybersecurity posture.
Importance of Encrypting Sensitive Data
Encrypting sensitive data is a key data loss prevention strategy that helps protect information from unauthorized access or theft. By converting data into a coded format that can only be deciphered with the proper encryption key, organizations can ensure that even if data is compromised, it remains unreadable and unusable to unauthorized parties.
Cloud-Based vs. On-Premises Data Loss Prevention Solutions
- Cloud-based data loss prevention solutions offer scalability, flexibility, and accessibility, making them ideal for companies with remote workforce or distributed operations.
- On-premises solutions provide greater control and customization options, allowing organizations to tailor their data loss prevention measures to specific security requirements and compliance standards.
- Both solutions have their advantages and limitations, depending on the organization’s size, industry, and data protection needs.
Legal and Financial Implications of Data Breach
Companies without proper data loss prevention measures in place may face severe legal consequences, including fines, lawsuits, and damage to their reputation. The financial impact of a data breach can be significant, with costs associated with incident response, regulatory fines, customer compensation, and loss of business.
Security Audits
Security audits play a crucial role in assessing the effectiveness of data protection measures implemented by companies. These audits involve a comprehensive evaluation of the organization’s security protocols, systems, and processes to identify potential vulnerabilities and ensure compliance with industry regulations.
Key Areas Evaluated in Security Audits
- Network Security: Assessing the strength of firewalls, intrusion detection systems, and other network security measures in place to protect against unauthorized access.
- Application Security: Evaluating the security of software applications to prevent exploitation of vulnerabilities that could lead to data breaches.
- Physical Security: Inspecting physical access controls, surveillance systems, and security measures at data centers or office locations to prevent unauthorized access to sensitive information.
- Compliance: Verifying that the company’s security practices align with industry standards and regulatory requirements to avoid legal consequences.
- Security Policies and Procedures: Reviewing the organization’s security policies, incident response plans, and employee training programs to ensure they are up to date and effective.
Vendor Risk Management
Vendor risk management plays a crucial role in ensuring data protection for companies. It involves assessing and mitigating the potential risks associated with third-party vendors who have access to sensitive company data.
Strategies for Assessing and Mitigating Risks
- Conduct thorough due diligence before engaging with any vendor, including background checks and reviews of their security protocols.
- Implement clear contractual agreements that outline data protection requirements and responsibilities.
- Regularly monitor and audit vendor activities to ensure compliance with security standards.
- Require vendors to provide evidence of their own cybersecurity measures and certifications.
Examples of Incidents Caused by Poor Vendor Risk Management
- In 2013, Target suffered a massive data breach due to hackers gaining access through a third-party HVAC vendor with weak security protocols.
- In 2019, Capital One experienced a data breach exposing over 100 million customer records, attributed to a misconfigured firewall by a cloud service provider.
- In 2020, EasyJet faced a data breach compromising the personal information of 9 million customers, linked to a cyber-attack on a third-party IT provider.
Emerging Technologies
AI and blockchain technologies are revolutionizing data protection for companies, offering advanced solutions to safeguard sensitive information in the digital age. Companies can harness these technologies to strengthen their data security measures and stay ahead of cyber threats. Let’s delve into how AI and blockchain are impacting data protection and explore innovative solutions in this realm.
AI-Powered Threat Detection
AI plays a crucial role in enhancing cybersecurity by enabling real-time threat detection and response. Machine learning algorithms can analyze vast amounts of data to identify patterns and anomalies that may indicate a security breach. By leveraging AI-powered tools, companies can proactively detect and mitigate potential threats before they escalate.
- AI-driven Security Analytics Platforms: These platforms use machine learning algorithms to detect unusual activities and potential security risks in real-time, enabling organizations to respond swiftly to cyber threats.
- Behavioral Biometrics: AI-based systems can analyze user behavior patterns to verify identities and detect unauthorized access attempts, enhancing access control and preventing data breaches.
Blockchain for Immutable Data Protection
Blockchain technology provides a decentralized and immutable ledger that ensures the integrity and security of data. By storing information in a tamper-proof and transparent manner, companies can prevent unauthorized modifications and enhance data authenticity.
- Secure Data Sharing: Blockchain enables secure data sharing among authorized parties while maintaining data integrity, reducing the risk of data manipulation or unauthorized access.
- Smart Contracts: Utilizing blockchain-based smart contracts can automate data protection processes, such as access control and data encryption, ensuring compliance with security protocols.
Integration of AI and Blockchain
Companies can combine AI and blockchain technologies to create innovative solutions that offer comprehensive data protection capabilities. This integration allows for enhanced threat detection, secure data storage, and streamlined security operations.
By leveraging AI and blockchain technologies, companies can establish a robust defense against evolving cyber threats and safeguard their valuable data assets.
Data Privacy Policies
Data privacy policies play a crucial role in safeguarding sensitive information and ensuring compliance with regulations for companies. These policies outline how data is collected, used, stored, and shared, setting clear guidelines for maintaining confidentiality and protecting personal information.
Best Practices for Creating and Implementing Data Privacy Policies
- Develop a comprehensive policy that covers all aspects of data handling, including data collection, processing, storage, and sharing.
- Ensure that the policy is easily accessible to employees and stakeholders, making it clear and easy to understand.
- Regularly review and update the policy to adapt to changing regulations and emerging cybersecurity threats.
- Provide training to employees on data privacy best practices and the importance of compliance with the policy.
- Establish procedures for handling data breaches and incidents to mitigate risks and protect sensitive information.
Examples of Companies with Exemplary Data Privacy Policies and Their Impact on Customer Trust
- Apple: Known for its strong commitment to user privacy, Apple’s data privacy policies prioritize user control over their personal information, earning trust and loyalty from customers.
- Google: With transparent data practices and tools for users to manage their privacy settings, Google has built a reputation for prioritizing user data protection and security.
- Microsoft: Microsoft’s data privacy policies emphasize transparency, accountability, and user consent, building trust with customers and stakeholders.
Closure
As we conclude our exploration of best data protection practices for companies, it is clear that a comprehensive approach combining technical measures, legal adherence, and employee training is crucial in today’s digital landscape. By staying informed and proactive, organizations can fortify their defenses and protect their valuable assets from cyber threats.